Today, VMware Certification announced a change to the VMware Certified Professional (VCP) program with the institution of a recertification policy. The recertification policy is posted here:
http://mylearn.vmware.com/mgrReg/plan.cfm?plan=46667&ui=www_cert
In the policy post, it states that any VCP certification earned before March 10, 2013 needs to be recertified by March 10, 2015. Here are the three options for recertification:
- Take the current exam for your existing VCP certification solution track. For example, if you are a VCP3, you could take the current VCP5-Data Center Virtualization (VCP5-DCV) exam.
- Earn a new VCP certification in a different solution track. For example, if you are a VCP-Cloud, you could recertify by earning VCP5-Desktop (VCP5-DT) certification.
- Advance to the next level by earning a VMware Certified Advanced Professional (VCAP) certification. For example, if you are a VCP5-DCV you could earn VCAP5-DCA certification.
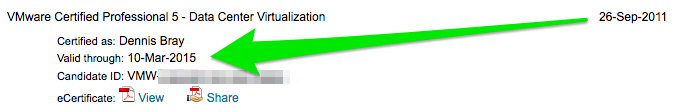
As is described in the recertification policy, VMware has added a note to our Mylearn transcripts:
In my case, I earned my VCP5-DCV in September of 2011, so I need to recertify within the next year. My transcript shows the expiration date:
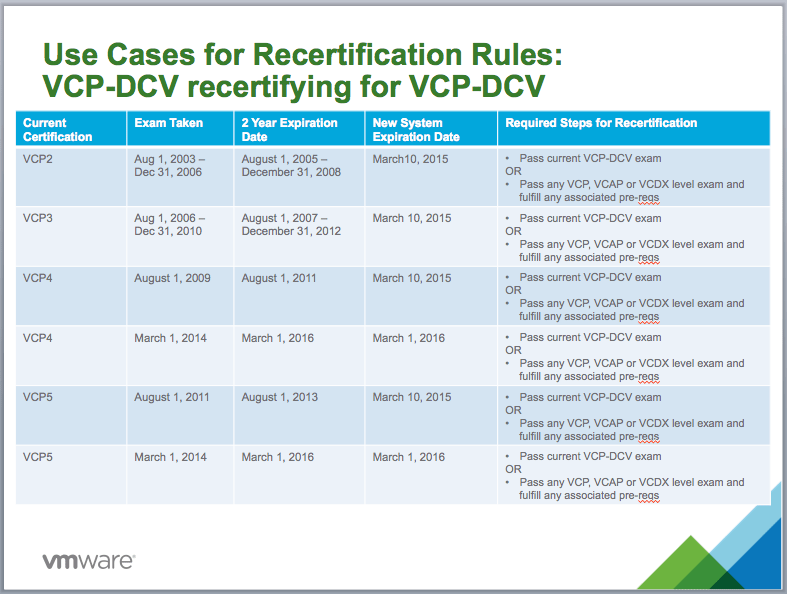
Here are use cases for recertification that were provided by VMware education:
I also have a VCP5-DT and a VCAP4-DCD that were earned in 2011. For me, I am looking at this as motivation to get my VCAP-DCD updated and make good on a goal of getting a VCAP-DCA before March 2015.
I support this kind of recertification requirement and appreciate the value of keeping in touch with the current technology.